Who might Bob,Alice be? ..well,real-life Bobs and Alices! Web browser/server for electronic transactions (e.g.,on-line purchases) on-line banking client/server DNS servers routers exchanging routing table updates other examples? Network Security 8-6
Network Security 8-6 Who might Bob, Alice be? … well, real-life Bobs and Alices! Web browser/server for electronic transactions (e.g., on-line purchases) on-line banking client/server DNS servers routers exchanging routing table updates other examples?
There are bad guys(and girls)out there! Q:What can a“bad guy”do? A:A lot!See section 1.6 -eavesdrop:intercept messages actively insert messages into connection impersonation:can fake (spoof)source address in packet (or any field in packet) "hijacking:“take over'”ongoing connection by removing sender or receiver,inserting himself in place denial of service:prevent service from being used by others (e.g.,by overloading resources) Network Security 8-7
Network Security 8-7 There are bad guys (and girls) out there! Q: What can a “bad guy” do? A: A lot! See section 1.6 eavesdrop: intercept messages actively insert messages into connection impersonation: can fake (spoof) source address in packet (or any field in packet) hijacking: “take over” ongoing connection by removing sender or receiver, inserting himself in place denial of service: prevent service from being used by others (e.g., by overloading resources)
Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography 8.3 Message integrity,authentication 8.4 Securing e-mail 8.5 Securing TCP connections:SSL 8.6 Network layer security:IPsec 8.7 Securing wireless LANs 8.8 Operational security:firewalls and IDS Network Security 8-8
Network Security 8-8 Chapter 8 roadmap 8.1 What is network security? 8.2 Principles of cryptography 8.3 Message integrity, authentication 8.4 Securing e-mail 8.5 Securing TCP connections: SSL 8.6 Network layer security: IPsec 8.7 Securing wireless LANs 8.8 Operational security: firewalls and IDS
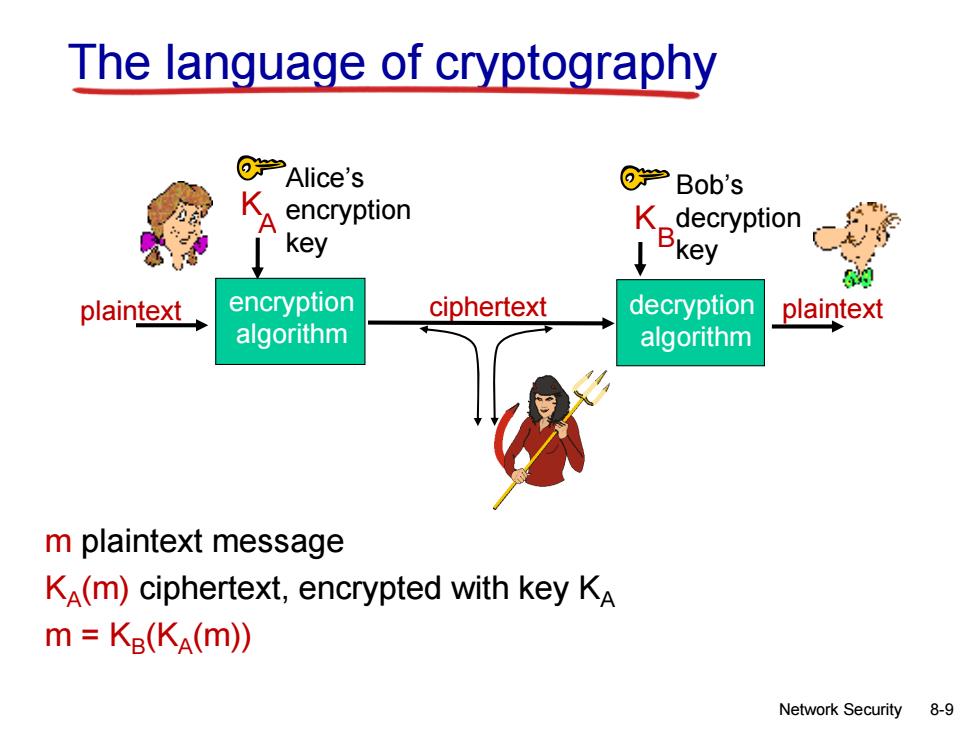
The language of cryptography @→Alice's @学Bob's encryption K_decryption key Bkey plaintext encryption ciphertext decryption plaintext algorithm algorithm m plaintext message KA(m)ciphertext,encrypted with key KA m KB(KA(m)) Network Security 8-9
Network Security 8-9 The language of cryptography m plaintext message KA (m) ciphertext, encrypted with key K A m = KB (KA (m)) plaintext ciphertext plaintext KA encryption algorithm decryption algorithm Alice’s encryption key Bob’s decryption key K B
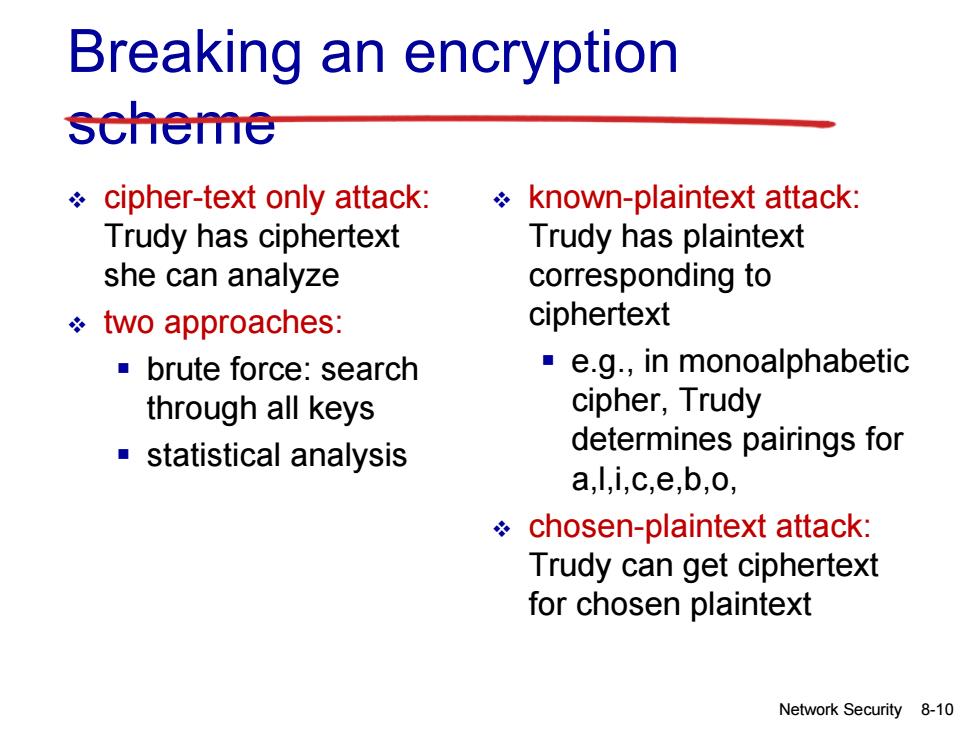
Breaking an encryption scheme cipher-text only attack: known-plaintext attack: Trudy has ciphertext Trudy has plaintext she can analyze corresponding to two approaches: ciphertext ■brute force:search e.g.,in monoalphabetic through all keys cipher,Trudy statistical analysis determines pairings for a,l,i,c,e,b,o, chosen-plaintext attack: Trudy can get ciphertext for chosen plaintext Network Security 8-10
Network Security 8-10 Breaking an encryption scheme cipher-text only attack: Trudy has ciphertext she can analyze two approaches: brute force: search through all keys statistical analysis known-plaintext attack: Trudy has plaintext corresponding to ciphertext e.g., in monoalphabetic cipher, Trudy determines pairings for a,l,i,c,e,b,o, chosen-plaintext attack: Trudy can get ciphertext for chosen plaintext